
You are viewing documentation for KubeSphere version:v3.0.0
KubeSphere v3.0.0 documentation is no longer actively maintained. The version you are currently viewing is a static snapshot. For up-to-date documentation, see the latest version.
Create a DevOps Kubeconfig on AWS
If you have trouble deploying applications into your project when running a pipeline on your AWS cluster with KubeSphere installed, it may be caused by the issue of DevOps kubeconfig. This tutorial demonstrates how to create a DevOps kubeconfig on AWS.
Prerequisites
- You have an AWS cluster with KubeSphere installed. For more information about how to install KubeSphere on AWS, refer to Deploy KubeSphere on AWS EKS.
- You have enabled the KubeSphere DevOps system.
- You have a project available for deploying applications. This tutorial uses the project
kubesphere-sample-devas an example.
Create a DevOps Kubeconfig
Step 1: Create a Service Account
-
Create a
devops-deploy.yamlfile on your AWS cluster and enter the following contents.--- apiVersion: v1 kind: ServiceAccount metadata: name: devops-deploy namespace: kubesphere-sample-dev --- apiVersion: rbac.authorization.k8s.io/v1 kind: Role metadata: name: devops-deploy-role namespace: kubesphere-sample-dev rules: - apiGroups: - "*" resources: - "*" verbs: - "*" --- apiVersion: rbac.authorization.k8s.io/v1 kind: RoleBinding metadata: name: devops-deploy-rolebinding namespace: kubesphere-sample-dev roleRef: apiGroup: rbac.authorization.k8s.io kind: Role name: devops-deploy-role subjects: - kind: ServiceAccount name: devops-deploy namespace: kubesphere-sample-dev -
Run the following command to apply the YAML file.
kubectl apply -f devops-deploy.yaml
Step 2: Get the Service Account Token
-
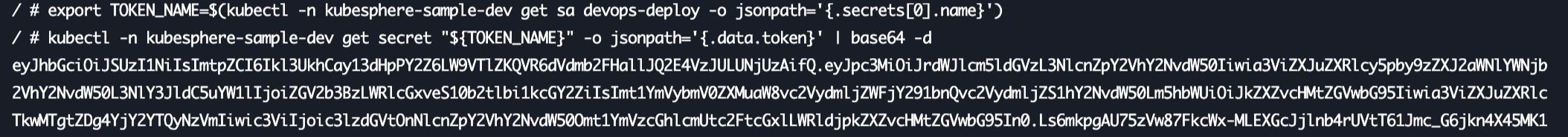
Run the following command to get the Service Account token.
export TOKEN_NAME=$(kubectl -n kubesphere-sample-dev get sa devops-deploy -o jsonpath='{.secrets[0].name}') kubectl -n kubesphere-sample-dev get secret "${TOKEN_NAME}" -o jsonpath='{.data.token}' | base64 -d -
The output is similar to the following:
Step 3: Create a DevOps kubeconfig
-
Log in to your KubeSphere console of the AWS cluster and go to your DevOps project. Go to Credentials under Project Management, and then click Create. You can name this kubeconfig based on your needs.
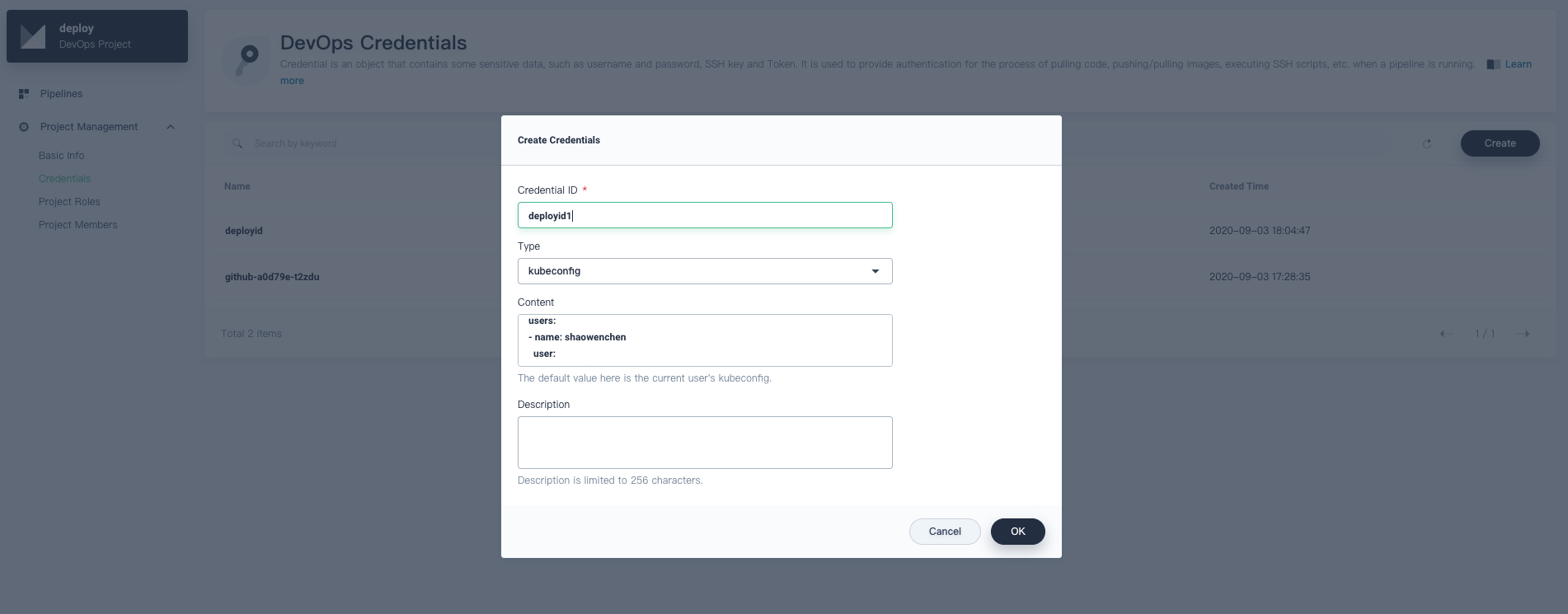
-
In the Content text box, pay attention to the following contents:
user: client-certificate-data: LS0tLS1CRUdJTiBDRVJUSUZJQ0FUR... client-key-data: LS0tLS1CRUdJTiBQUk...You have to replace them with the token retrieved in step 2, then click OK to create the kubeconfig.
user: token:eyJhbGciOiJSUzI1NiIsImtpZCI6Ikl3UkhCay13dHpPY2Z6LW9VTlZKQVR6dVdmb2FHallJQ2E4VzJULUNjUzAifQ.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJrdWJlc3BoZXJlLXNhbXBsZS1kZXYiLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlY3JldC5uYW1lIjoiZGV2b3BzLWRlcGxveS10b2tlbi1kcGY2ZiIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VydmljZS1hY2NvdW50Lm5hbWUiOiJkZXZvcHMtZGVwbG95Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZXJ2aWNlLWFjY291bnQudWlkIjoiMjM0ZTI4OTUtMjM3YS00M2Y5LTkwMTgtZDg4YjY2YTQyNzVmIiwic3ViIjoic3lzdGVtOnNlcnZpY2VhY2NvdW50Omt1YmVzcGhlcmUtc2FtcGxlLWRldjpkZXZvcHMtZGVwbG95In0.Ls6mkpgAU75zVw87FkcWx-MLEXGcJjlnb4rUVtT61Jmc_G6jkn4X45MK1V_HuLje3JZMFjL80QUl5ljHLiCUPQ7oE5AUZaUCdqZVdDYEhqeFuGQb_7Qlh8-UFVGGg8vrb0HeGiOlS0qq5hzwKc9C1OmsXHS92yhNwz9gIOujZRafnGKIsG6TL2hEVY2xI0vvmseDKmKg5o0TbeaTMVePHvECju9Qz3Z7TUYsr7HAOvCPtGutlPWLqGx5uOHenOdeLn71x5RoS98xguZoxYVollciPKCQwBlZ4zWK2hzsLSNNLb9cZpxtgUVyHE0AB0e86IHRngnnNrzpp1_pDxL5jw/Note
Make sure you use your own token.













 Previous
Previous
